NEXTGEN-TV PROGRAMMING
NOW PLAYING
Starting on the hour every hour today
Coming up this Week
NEXTGEN-TV PROGRAMMING
NOW PLAYING
Starting on the hour every hour today
Coming up this Week

 |  Bharat Parshotam Bharat ParshotamHead Direct Delivery Absa |
 |  Nathalya Wani Sabu Nathalya Wani SabuExecutive Vice President PT. Bank Central Asia, Tbk |
 |  Aymen Ismail Aymen IsmailHead of Customer Engagement Solutions smart Europe GmbH |
 |  Sindhu Porwal Sindhu PorwalDeputy Vice President ICICI lombard |
 |  Emmanuel Omoike Emmanuel OmoikeTeam leader QPhoto Pty |
 |  Ben Oxford Ben OxfordHead of Digital Crisis Support Services Lifeline WA |
 |  Pooja Raiyani Pooja RaiyaniVice President ICICI Lombard GIC Ltd |
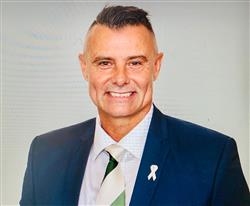
 |  Danny Singer Danny SingerFounder& Chief Product Officer Noetica |
 |  Nuryanto - Nuryanto -Head of CSM Operation Bukalapak |
 |  Bill Quiseng Bill QuisengChief Experience officer Bill Quiseng dot com |
I am checking out all the amazing and daily updated content on ContactCenterWorld.com and networking with professionals worldwide
Send To Friends Post On My Wall